Blog
7 Common Pitfalls When Adopting Zero Trust Security
Zero Trust security is rapidly transforming the cybersecurity landscape. It moves away from traditional perimeter-based security models. In this approach, every connection attempt is continuously verified before granting resource access.56% of global organizations say...
4 Ways Small Businesses Can Leverage Copilot for Microsoft 365
What are some of the key differentiators that can propel small businesses forward? They include efficiency, productivity, and innovation. Microsoft has expanded the availability of one of its most dynamic tools to SMBs. A tool that can be a real game-changer for...
Introducing the New Microsoft Planner (Everything You Need to Know)
Calendars, task lists, and project planning are important business tools. Many people use Microsoft’s apps to power these processes. Including Planner, Microsoft To Do, and Project for the web.These tools help keep processes on track and enable task accountability....
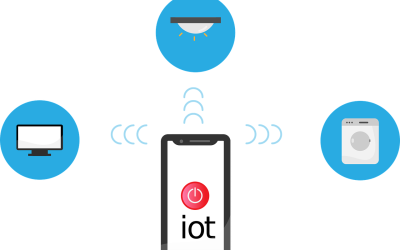
How to Properly Deploy IoT on a Business Network
The Internet of Things (IoT) is no longer a futuristic concept. It's rapidly transforming industries and reshaping how businesses operate. IoT is a blanket term to describe smart devices that are internet enabled. One example is smart sensors monitoring production...
Here Are 5 Data Security Trends to Prepare for in 2024
With cyber threats evolving at an alarming pace, staying ahead of the curve is crucial. It’s a must for safeguarding sensitive information. Data security threats are becoming more sophisticated and prevalent. The landscape must change to keep up. In 2024, we can...
Google & Yahoo’s New DMARC Policy Shows Why Businesses Need Email Authentication… Now
Have you been hearing more about email authentication lately? There is a reason for that. It’s the prevalence of phishing as a major security threat. Phishing continues as the main cause of data breaches and security incidents. This has been the case for many years.A...
Beware of Deepfakes! Learn How to Spot the Different Types
Have you ever seen a video of your favorite celebrity saying something outrageous? Then later, you find out it was completely fabricated? Or perhaps you've received an urgent email seemingly from your boss. But something felt off.Welcome to the world of deepfakes....
10 Most Common Smart Home Issues (and How to Fix Them)
Back when you were a kid, living in a “smart home” probably sounded futuristic. Something out of Back to the Future II or The Jetsons. Well, we don’t yet have flying cars, but we do have video telephones as well as smart refrigerators and voice-activated lights.But...
Using Technology to Run a Home-Based Business
Thanks to the wonderful creation that is the internet, just about anyone can set up and run a home-based business. You just need a phone, a laptop, and some software programmes. How exciting!
What Is Microsoft Security Copilot? Should You Use It?
It can be challenging to keep up with the ever-evolving cyber threat landscape. Companies need to process large amounts of data. As well as respond to incidents quickly and effectively. Managing an organization's security posture is complex.That's where Microsoft...
Smart Tactics to Reduce Cloud Waste at Your Business
Cloud computing has revolutionized the way businesses operate. It offers scalability, flexibility, and cost-efficiency. But cloud services also come with a downside: cloud waste.Cloud waste is the unnecessary spending of resources and money on cloud services. These...
Eye-opening Insights from the 2023 Annual Cybersecurity Attitudes and Behaviors Report
We are living in an era dominated by digital connectivity. You can't overstate the importance of cybersecurity. As technology advances, so do the threats that lurk in the online world.Often, it’s our own actions that leave us most at risk of a cyberattack or online...
Contact Us
We are here to answer your questions and provide advice that will help you understand your systems better. We add the personal touch to technology by making sure one of our team always picks up the phone, rather than an automated message as your first greeting. We always respond quickly to first contact emails which, for you, gives reassurance we will act quickly to resolve any issues and get you back on track.
Book a Discovery Call on 0113 531 5400 or leave your details on the contact form below: